Feature Creep in Backup: Evolution or Escape Strategy?
Table of contents
- When Success Breeds Complexity: A Cautionary Tale
- The Market Reality: Evolution or Desperation?
- Data Management: Genuine Transformation or Marketing Makeover?
- Cybersecurity and Backup: Together or Separate?
- The Real Cost of Feature Creep
- The Path Forward: Specialized Excellence
- Key Takeaways for C-Level Executives
- Experience Backup Without the Bloat
The backup industry is experiencing an identity crisis. Some vendors are adding security features, others are pivoting to data management, and still others are trying to be everything to everyone. Storware is choosing a different path—one focused on doing one thing exceptionally well.

When Success Breeds Complexity: A Cautionary Tale
Those who remember the era of burning CDs and DVDs certainly encountered Nero Burning ROM. Initially, it was a classic disc-burning program that excelled at its core function, leaving competitors far behind. Its success stemmed from high specialization and laser focus on solving one problem perfectly.
However, over time, the manufacturer began adding features: multimedia project creation, video editing, file conversion, and more. The intentions seemed sound—adapt the product to a changing market. Unfortunately, expanding the program’s capabilities made it increasingly cumbersome and complicated for users who only needed basic burning functions. Installation consumed significant disk space, and the interface lost its intuitive nature. Competitors who maintained narrow specialization quickly capitalized on this bloat. While the software still exists today, its glory days are long behind it.
This phenomenon, known as feature creep, is observed across IT market segments, where original utility becomes obscured by an excess of options. According to Pendo’s 2019 Feature Adoption Report, approximately 80% of features in the average software product are rarely or never used. Additionally, Gartner estimates that by 2023, I&O leaders will overspend $750 million specifically on unused features of ITSM tools. A similar fate may await some products introduced as backup and disaster recovery systems.
The Market Reality: Evolution or Desperation?
Data protection solution providers are indeed expanding their product portfolios—this is a natural feature of market dynamics. Stagnation would signal danger, and competition demands constant forward movement. However, a fundamental question arises: not so much about the direction of change, but about its justification and reasonableness.
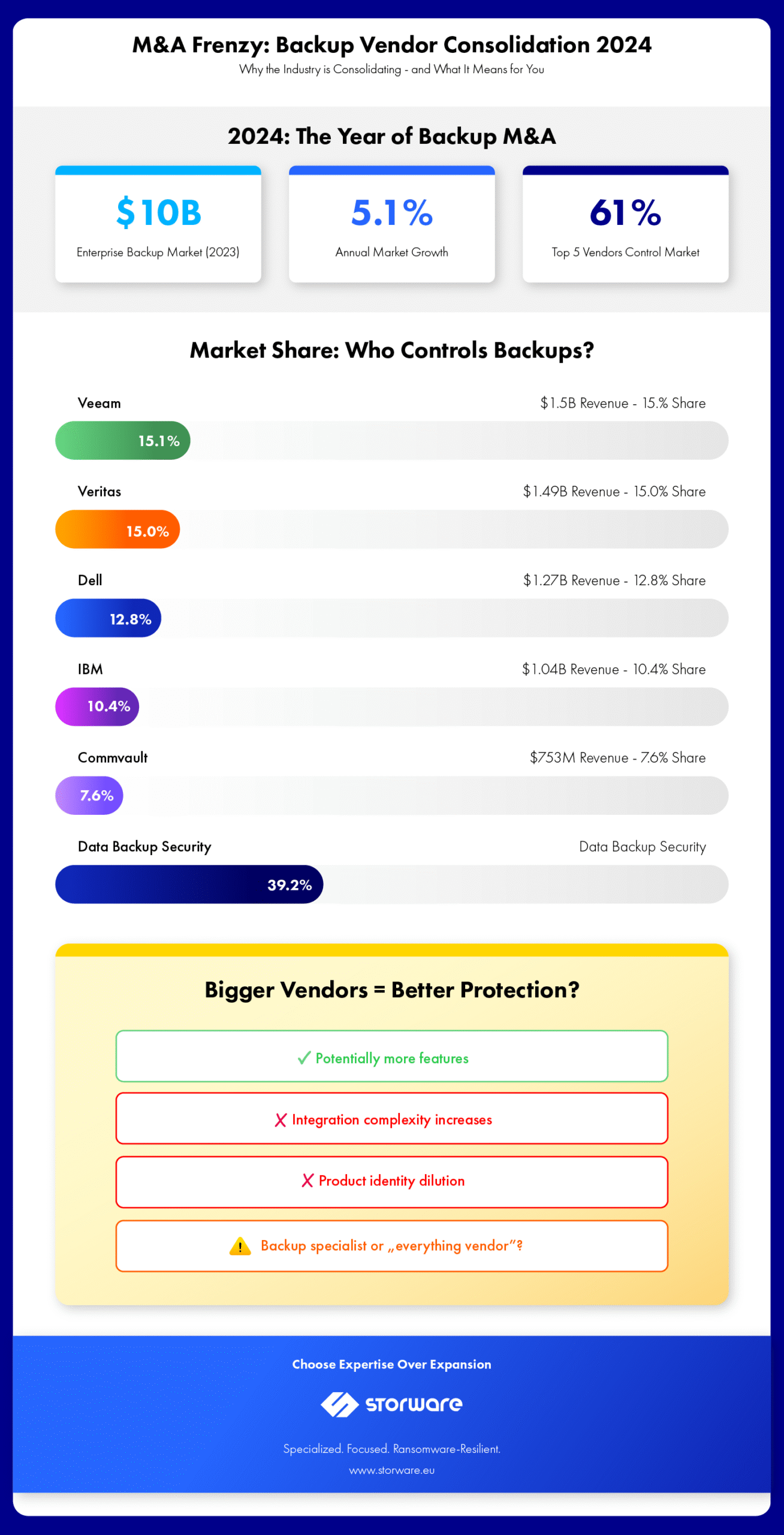
The enterprise backup and recovery market grew 5.1% in 2023, reaching nearly $10 billion in total revenue. Yet 2024 was defined by aggressive consolidation, with major players like Cohesity, Veeam, and Commvault acquiring competitors and smaller vendors to rapidly expand capabilities. This raises critical questions for C-level executives: Is this consolidation building genuine value, or is it a desperate attempt to remain relevant in an evolving landscape?
Data Management: Genuine Transformation or Marketing Makeover?
Many innovations reaching the market spark controversy and leave customers confused. A particularly interesting case is traditional backup vendors positioning themselves as data management leaders. At first glance, this appears to be natural evolution—a transition from pure protection to strategic information governance.
Backup vendors undoubtedly possess solid knowledge about storing and recovering data. However, data management represents an entirely different level of sophistication. It encompasses governance, cataloging, establishing data lineage, ensuring compliance, and even monetizing information. These are areas requiring deep, specialized competencies that traditional backup has never needed to address.
True credibility depends on concrete facts. Has the vendor actually built new capabilities, or merely rebranded old functions? Do they possess teams with genuine experience? Does their solution integrate organically with the client’s existing infrastructure, or does it force costly system replacement? Is the positioning based on in-depth case studies and evidence of effectiveness, or on marketing declarations?
One quick path to expert status is acquiring smaller players offering specialized data protection solutions. This is a natural strategic move, though mergers yield very different results. Moreover, there’s no guarantee that the acquired player possesses solutions at the segment leaders’ level, or that their technology will be compatible with the acquirer’s ecosystem. Perhaps it’s better to stick with specialized tools—both for backup and data management?
The fundamental question remains: To what extent is the shift from backup to data management a desperate move, and to what extent is it natural business evolution? Some experts express the view that it’s primarily an escape route—a last chance for survival in a market dominated by specialists.
Cybersecurity and Backup: Together or Separate?
For many years, data protection and cybersecurity functioned as two independent domains. The situation changed drastically with rising ransomware gang activity. Cybercriminals shifted their strategy—instead of only encrypting data, they also try to cut victims off from backup copies. When there’s no alternative, forcing ransom payment becomes significantly more effective.
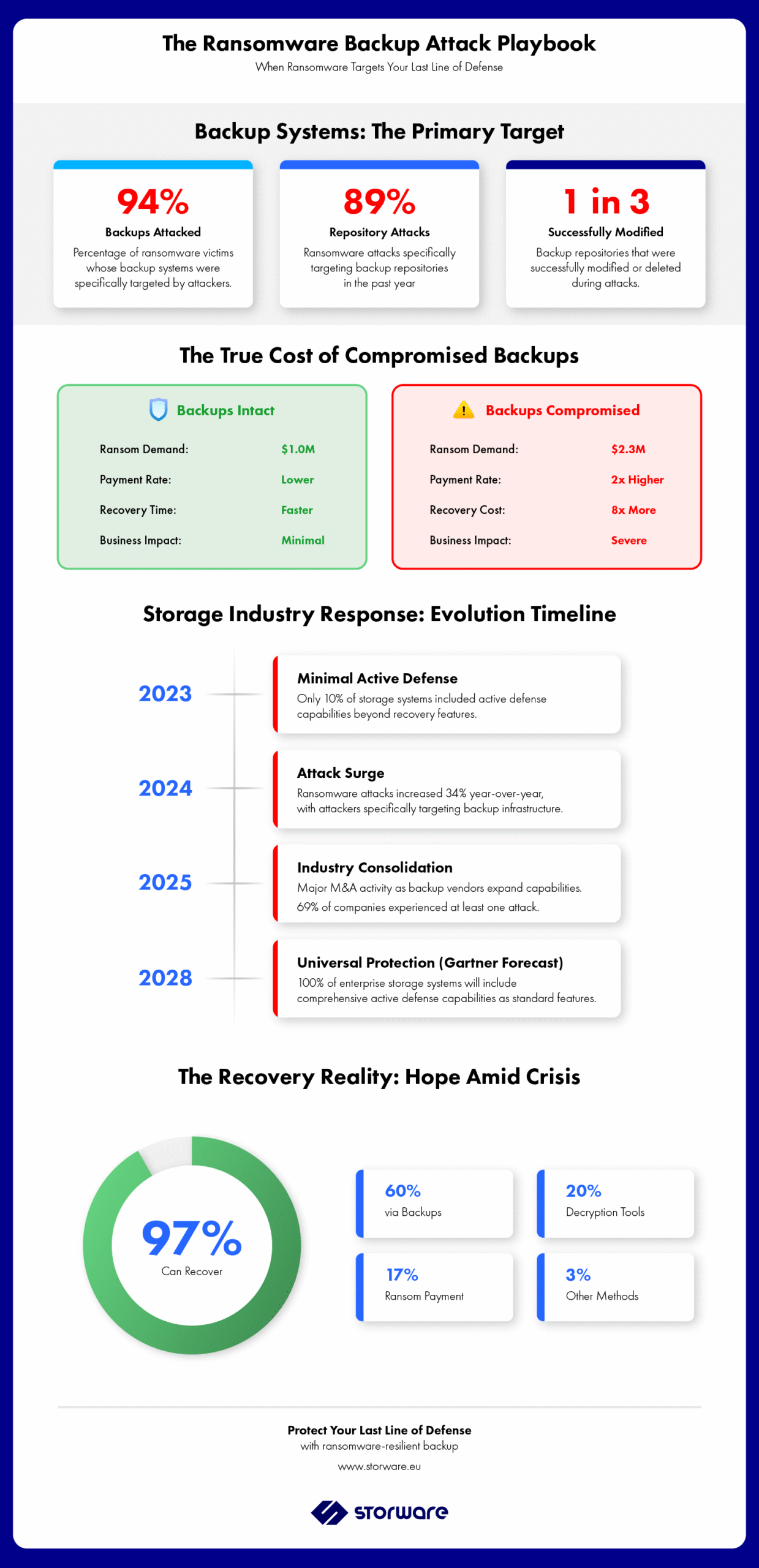
The scale of the problem is alarming. According to Sophos research, 94% of attacked companies confirm that hackers attempted to destroy or damage their backups. When backups are compromised, the median ransom demand jumps to $2.3 million—more than double the $1 million demanded when backups remain intact. More recent research from Veeam reveals that 89% of ransomware attacks in the past year targeted the backup repository, with a third of repositories modified or deleted. For C-level executives, this represents not just a technical challenge but an existential business risk: companies whose backups are compromised are nearly twice as likely to pay the ransom, and recovery costs are eight times higher.
The Storage Industry’s Response
In response to this threat, leading disk array vendors introduced advanced defense mechanisms. Their portfolios include immutable snapshots, WORM (Write Once, Read Many) functions, and multi-factor authentication for data deletion operations. A commonly applied solution is also “air gap“—physical isolation of backups from networks and primary mass storage systems.
Gartner forecasts indicate that by 2028, 100% of enterprise-class storage systems will standardly offer active defense elements—up from just 10% in early 2023. This prediction reflects the severity of the threat landscape and the imperative for proactive protection measures.
Where Do We Draw the Line?
Backup solution providers are also introducing changes. Some manufacturers are attempting to broadly introduce functionalities found in IT security systems. While immutable backups and air-gapped storage have become practically standard, further expansion of the offered spectrum raises an important question: where is the boundary?
Some manufacturers offer backup and threat detection tools within one platform, identifying unusual data patterns and user activity. There are clear attempts to merge the cybersecurity and backup markets. To a large extent, financial considerations drive this—data protection and recovery system providers want to be close to security to reach significantly larger budgets. The global information security market is expected to reach $292 billion by 2028, growing at a CAGR of 11.7%.
Not everyone agrees with this trend. Critics point to fundamental differences in system objectives. Cybersecurity systems should focus on prevention—stopping attacks before they occur. Backup has an entirely different role: restoring data in pristine condition after an attack. Its task isn’t threat detection, but being the ultimate line of defense.
The Case for Integration Over Consolidation
From this perspective, a much better solution than full consolidation is the integration of tools from security and backup sectors, which allows maintaining each system’s specialization. Storware operates on the assumption that the optimal solution is logical system integration—so they can “communicate” and react together—while maintaining physical separation with backups stored independently.
Many companies are increasingly moving toward architectures where backup has its dedicated security tools but simultaneously integrates with SIEM and threat detection platforms. This hybrid model allows comprehensive protection without sacrificing specialization.
Specialization has its business and technical logic. IT security system providers invest enormous sums in R&D, recruit the best specialists from the market, and track and analyze hacker behavior. For a backup provider, such rivalry would be extremely costly. Sometimes strategic partnerships prove more effective than internal scope expansion. They allow offering comprehensive solutions without dispersing resources. Importantly, clients typically accept the integration of multiple solutions if they communicate well and operate harmoniously.
While the boundaries between backup and cybersecurity are indeed blurring, this doesn’t mean both areas should completely merge.
The Real Cost of Feature Creep
The financial impact of feature creep extends far beyond initial development costs. Research shows that developers spend an average of 17.3 hours per week dealing with bad code, errors, debugging, and refactoring, with an additional 13.5 hours per week on technical debt—the accumulated cost of development decisions that increase future maintenance burden.
For enterprises, this translates to:
- Delayed time-to-market: Projects experiencing feature creep face average delays of 6 months or more
- Increased operational complexity: Managing bloated systems requires larger IT teams and more extensive training
- Higher total cost of ownership: Feature-rich systems demand more resources for maintenance, updates, and troubleshooting
- Reduced competitive agility: Complex systems are harder to adapt to rapidly changing business needs
The ransomware threat amplifies these costs. Organizations with complex, feature-laden backup systems struggle more during attacks because:
- Longer recovery times due to system complexity
- Difficulty verifying backup integrity across numerous features
- Increased attack surface for cybercriminals to exploit
- Higher training requirements for disaster recovery procedures

The Path Forward: Specialized Excellence
Many backup solution providers make a similar mistake—instead of concentrating on what they do best, they’ve become slaves to feature additions. This creates a digital Frankenstein that’s difficult to maintain and very expensive. Storware doesn’t intend to use sophisticated terms like “Resilient Data Protection,” “Digital Fortress,” or “Bunker.” We want to be a manufacturer selling the key function—fast and recoverable backup—but always operating in a lightweight, efficient, and scalable manner.
Caution in this matter is entirely justified. It’s good when a vendor says “let’s do backup better” rather than pretending to be an expert in a field they’re still learning. Of course, adding features isn’t bad in itself. The problem appears when it leads to blurring the product’s identity and new categories prove difficult to master.
Key Takeaways for C-Level Executives
Market Consolidation Signals: The 2024 wave of backup vendor M&A activity—including major acquisitions by Cohesity, Veeam, and Commvault—indicates market uncertainty. Evaluate whether your current vendor’s acquisition strategy genuinely enhances capabilities or merely creates integration complexity.
The Ransomware Business Case: With 94% of ransomware attacks targeting backups and ransom demands doubling when backups are compromised ($2.3M vs. $1M), backup resilience isn’t just an IT issue—it’s a board-level financial risk requiring executive attention.
Storage Evolution Timeline: Gartner’s prediction that 100% of enterprise storage will have active defense capabilities by 2028 means vendors without these features will become obsolete. Factor this timeline into your infrastructure roadmap.
The Hidden Tax of Bloatware: Organizations waste $750 million annually on unused software features. When evaluating backup solutions, assess actual usage patterns versus marketed capabilities—complexity you don’t need is cost you shouldn’t bear.
Integration vs. Consolidation: Rather than seeking an all-in-one vendor, consider best-of-breed solutions with robust integration capabilities. This approach maintains specialized excellence while enabling comprehensive protection through interconnected systems.
Recovery as Strategic Priority: With 97% of organizations able to recover from ransomware using backups, recovery capabilities—not feature lists—should drive vendor selection. Focus on recovery time objectives (RTOs), recovery point objectives (RPOs), and validated recovery testing.
The backup industry stands at a crossroads. Those who chase every trend risk becoming bloated and ineffective. Those who maintain focus on core competencies—rapid, reliable, ransomware-resilient backup—will deliver the business continuity C-level executives actually need. In an era where data availability determines business survival, simplicity and reliability trump feature lists every time.
Experience Backup Without the Bloat
Storware Backup and Recovery delivers what enterprise organizations actually need: fast, reliable, ransomware-resilient data protection without unnecessary complexity. No feature creep. No identity crisis. Just focused excellence in backup and recovery. Download a free trial to test our specialized approach in your environment, or schedule a consultation with our backup experts to discuss your specific data protection challenges and recovery requirements.
