Data Security Uncompromising Protection for the Modern Business
Storware understands the criticality of data in today’s digital landscape. Data breaches can be devastating, leading to financial losses, reputational damage, and regulatory fines.
Cyberattacks are a constant threat. Traditional backups might not be enough. Storware delivers secure backups that are the cornerstone of your cyber resilience strategy. Our multi-layered protection safeguards your data across your entire physical, virtual and hybrid cloud environment, giving you complete peace of mind.

Future-Proof Your Data with Storware's Data Resilience
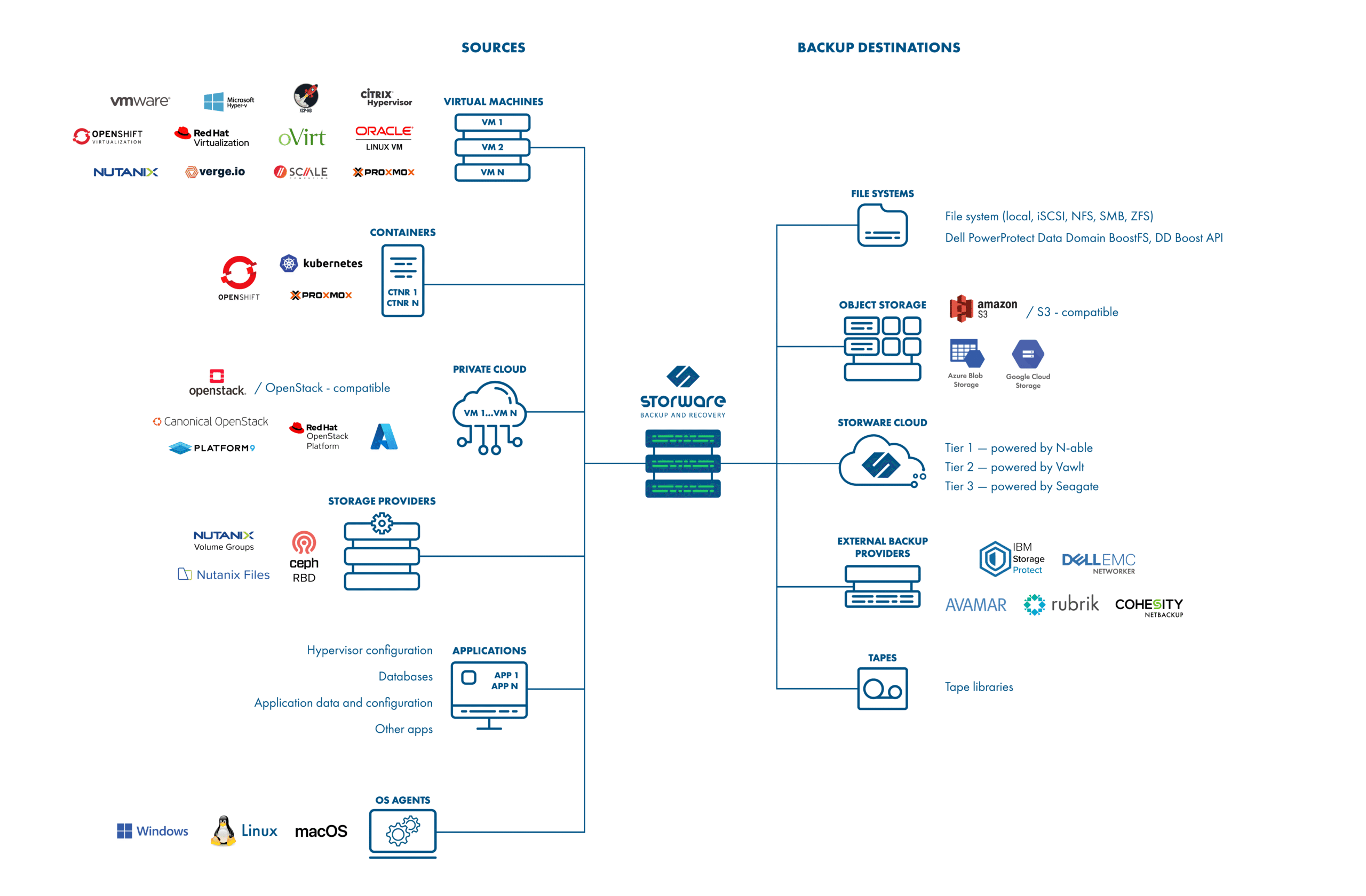
Data security today is the foundation of business continuity tomorrow. Enterprise organizations can’t afford ambiguity when it comes to data protection — they need a backup solution that is provably secure, verifiably recoverable, and consistently compliant across every layer of their infrastructure. Storware Backup and Recovery was built to deliver exactly that: comprehensive, multi-layered data security that covers your entire environment — on-premises, private cloud, hybrid cloud, or multi-hypervisor — under a single, unified platform.
Here’s how Storware protects your data against ransomware and unauthorized access:
- Immutable Backup Storage – Storware enforces write-once, tamper-proof backup storage on XFS-based destinations, ensuring that ransomware cannot encrypt, alter, or delete your backup data — even if it has already compromised your primary infrastructure. This is your last line of defense and it holds.
- Air-Gap Data Protection – Beyond immutability, Storware supports air-gapped backup configurations — including integration with Rubrik Managed Volumes, Catalogic vStor, and isoLayer — physically isolating your recovery point from the attack surface. A backup that an attacker cannot reach is a backup that will actually save you.
- Secondary Backup Destinations (Backup Copy) – Storware’s policy engine allows you to define secondary backup destinations — storing redundant copies in geographically or logically separated locations. Whether it’s cross-site replication or cloud offload to Seagate Lyve Cloud, Vawlt, or N-able, your data is never in a single point of failure.
- Policy-Based Retention with Granular Control – Retention policies in Storware are fully customizable: define version-based and time-based retention for both full and incremental backups, independently. This gives IT teams precise control over how long clean recovery points are preserved — critical when dealing with ransomware that deliberately delays activation to corrupt older backups.
- Universal Coverage Across Your Entire Infrastructure – From VMware vSphere and Microsoft Hyper-V, through Red Hat OpenShift, OpenStack, Nutanix AHV, Proxmox, and VergeOS — Storware protects workloads across heterogeneous environments under one license. There are no gaps in your protection posture because there are no unsupported platforms left unmanaged