Data Sovereignty & Backup: How to Reduce RTO and Control Your Data
Table of contents
- Defining Independence: What Technological Sovereignty Actually Means
- Digital Sovereignty: Do Your Data Really Belong to You?
- Backup Close to Home: Why RTO Is a Sovereignty Problem
- Marketing Goliath and the European Backup Alternative
- The Gartner Magic Quadrant: Useful Guide or Compliance Shortcut?
- Key Takeaways
- Frequently Asked Questions
- Sources & Further Reading
European organisations are talking louder than ever about “technological sovereignty” and “data sovereignty.” But is this mere PR positioning, or the beginning of a genuine structural shift in enterprise IT?
Donald Trump’s second presidency and its unpredictable trade posture have accelerated what was already a quiet movement: European businesses are seriously re-evaluating their dependence on US-based technology ecosystems. The question is no longer theoretical — it is operational. Do we have real alternatives, and are we architecting our infrastructure to use them?
Defining Independence: What Technological Sovereignty Actually Means
Technological sovereignty means the ability of a state or region — such as the EU — to make independent decisions about critical IT infrastructure, free from paralyzing dependence on external actors. It is not about digital isolation or manufacturing everything locally. The goal is to build the capability and competence so that no external party can suddenly “pull the plug” or impose terms that conflict with our economic interests or security requirements.
Where Ideals Meet Pragmatism
Let us be realistic: full technological autocracy is nearly impossible in a globalised world. There is no credible European alternative for commodity operating systems, advanced semiconductor architectures, or hyperscale storage platforms — at least not yet.
There are, however, domains where Europe performs extremely well. Cybersecurity and data protection are among them. Local vendors offer solutions that not only match their US counterparts technically, but frequently surpass them in compliance with Europe’s dense regulatory landscape — GDPR, NIS2, DORA, and the EU Data Act, fully applicable since September 2025.

Digital Sovereignty: Do Your Data Really Belong to You?
We live in a time where geopolitics and jurisdictional conflicts strike directly at digital infrastructure. During sanctions regimes, governments can swiftly seize, block, or cut access to cloud services — paralyzing business operations. For organisations reliant on non-sovereign providers, the question is no longer “if” disruption will occur, but “when”, and how costly it will be.
A thoughtful backup strategy — executed in a sovereign cloud or on-premises — is more than a safety net today. It is the foundation of digital independence.
The CLOUD Act: Jurisdiction Follows the Provider, Not the Server
Here is the core problem that too many European IT leaders still underestimate: simply having a backup does not mean you have full legal, physical, or technological control over it.
If your backup resides on infrastructure belonging to companies subject to US law — Microsoft, Google, Amazon — you are exposed to the US CLOUD Act (Clarifying Lawful Overseas Use of Data Act, 2018). Under this statute, US authorities can compel access to your data regardless of whether the physical server sits in Warsaw, Berlin, or Paris. What matters is the jurisdiction of the provider, not the location of the hardware.
The risk was compounded in April 2024 when FISA Section 702 was reauthorised with expanded scope, now covering virtually any entity with access to equipment capable of transmitting or storing electronic communications. Together, the CLOUD Act and FISA 702 create a layered system of US government access that bypasses geography entirely.
On the other side of the Atlantic, GDPR Article 48 states the opposite: EU data cannot be handed over to a non-EU authority simply because that authority issues a court or administrative order. A formal international treaty — such as a Mutual Legal Assistance Treaty (MLAT) — is normally required. This creates an unresolved legal conflict at the heart of every European organisation using a US cloud provider, regardless of where its servers are physically located.
This Is Now a Compliance Obligation, Not Just a Preference
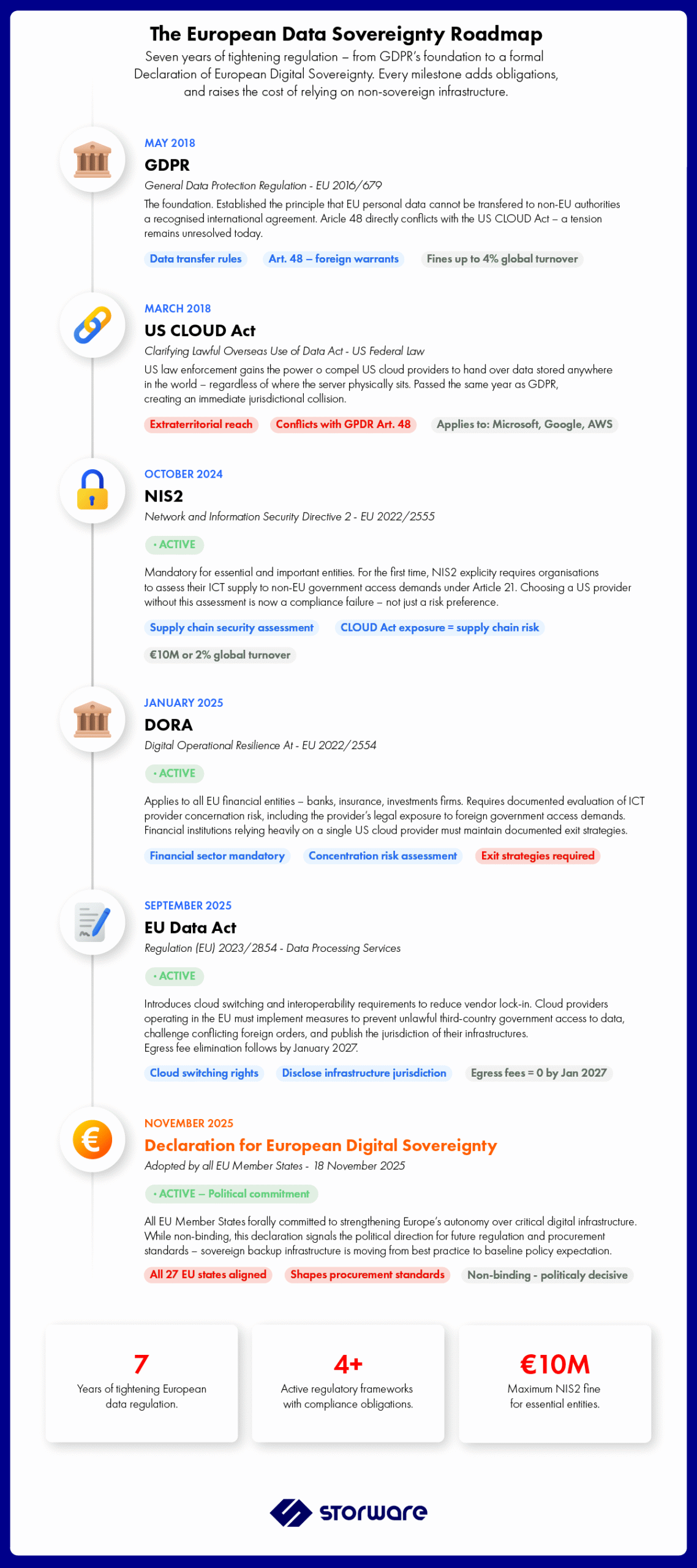
Critically, this risk is now baked directly into European regulatory requirements:
- NIS2 (applicable since October 2024) requires essential and important entities to assess their ICT supply chain’s exposure to non-EU government access demands under Article 21. An organisation that has not evaluated its US cloud provider’s CLOUD Act exposure may already be non-compliant — with fines reaching €10 million or 2% of global annual turnover.
- DORA (applicable since January 2025) requires financial entities to evaluate ICT provider concentration risk, assess confidentiality commitments, and maintain documented exit strategies for critical ICT relationships. The CLOUD Act creates a specific concentration risk that DORA explicitly requires financial institutions to address.
- The EU Data Act, fully applicable since September 2025, requires cloud providers operating in the EU to implement measures preventing unlawful third-country government access and to disclose the jurisdiction of their infrastructure.
- On 18 November 2025, all EU Member States signed the Declaration for European Digital Sovereignty, a political commitment to reduce strategic digital dependencies — the clearest signal yet that sovereign infrastructure is becoming baseline policy expectation, not optional best practice.
A Real-World Warning: When Data Becomes Hostage
This is not hypothetical. A Dutch bank with Russian capital provides a cautionary example. Following Russia’s invasion of Ukraine, the institution was subjected to sanctions, with its data held in Microsoft’s cloud. When a Dutch bankruptcy court demanded access to that data, Microsoft refused — citing that it was subject exclusively to US-imposed sanctions. The legal process stalled completely. Access to critical business records was cut off.
The lesson is unambiguous: in a collision between geopolitics and your cloud provider’s obligations, your infrastructure can become a hostage — and someone else holds the keys.
Backup Close to Home: Why RTO Is a Sovereignty Problem
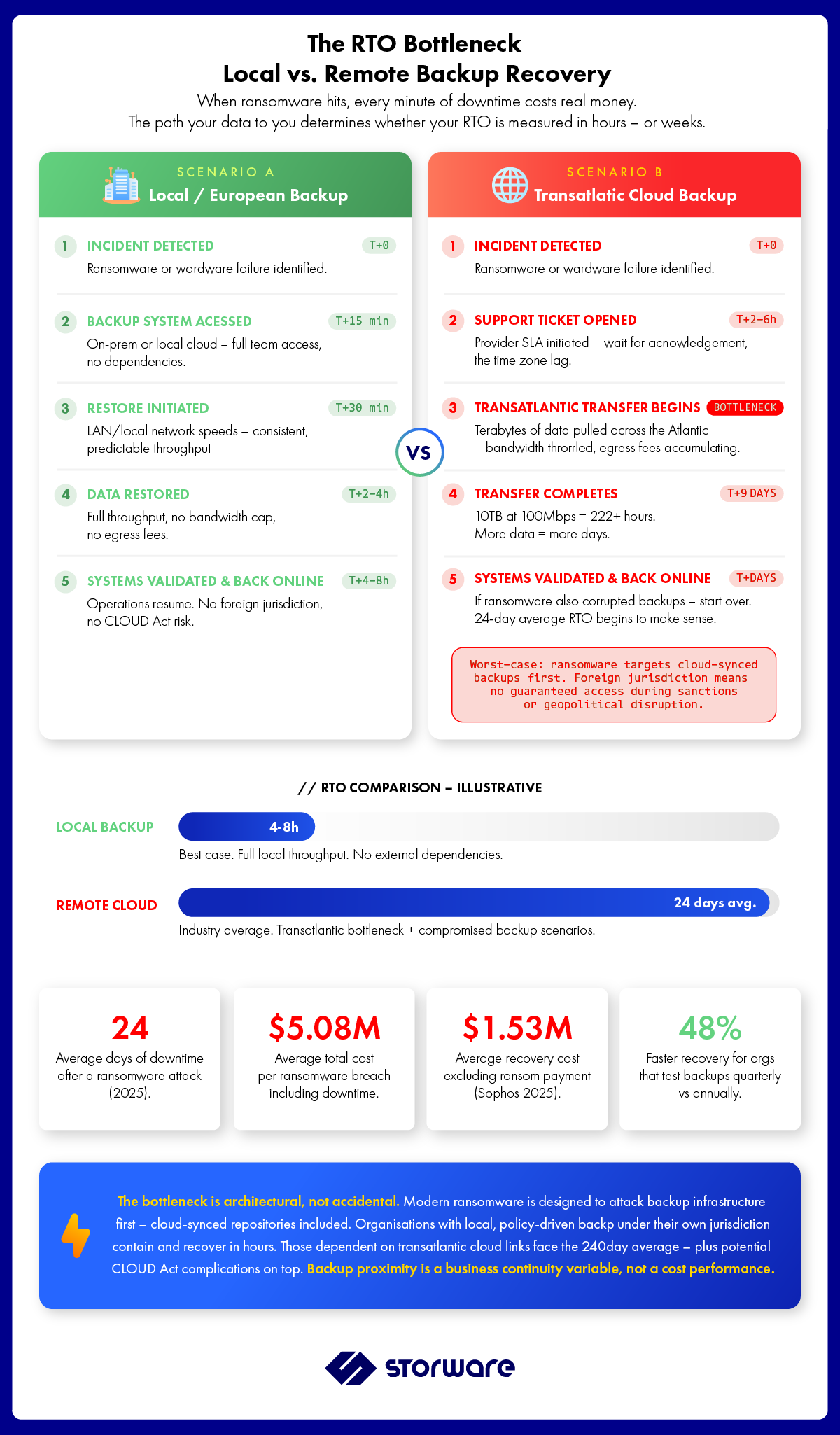
Most organisations think about backup only when something goes wrong: a server failure, a corrupted storage array, or a ransomware attack encrypting critical systems. When that happens, every minute counts.
The numbers are sobering. According to the 2025 Sophos State of Ransomware report, average organisational downtime following a ransomware attack remains around 24 days. Recovery costs — excluding any ransom payment — averaged $1.53 million in 2025. The total cost of a ransomware breach, including business interruption, legal exposure, and reputational damage, averaged $5.08 million per incident.
Against that backdrop, where your backup data physically lives — and how quickly you can restore from it — is not a procurement footnote. It is a core business continuity variable.
The Transatlantic Bottleneck
Many providers compete on low price while obscuring the fact that your data travels to servers on the other side of the Atlantic. This creates two compounding risks when disaster strikes.
The first is operational paralysis. Restoring terabytes across transatlantic links takes dramatically longer than local recovery, extending RTO from hours to days or weeks. Even at an effective throughput of 100 Mbps — a realistic outcome under latency and congestion — restoring a 10 TB dataset takes over 9 days under ideal conditions.
The second is legal and compliance exposure. Storing data outside your jurisdiction without full transparency over server location creates liability under GDPR, NIS2, and DORA. Modern ransomware is also specifically designed to target cloud-synced backup repositories first — meaning the safety net you think you have may already be compromised before the restore request is even initiated.
In regulated industries — banking, healthcare, critical infrastructure — the choice of backup provider has ceased to be a technical question. It is a strategic and legal one. As a Polish vendor operating within the European regulatory framework, Storware is natively aligned with GDPR, NIS2, and DORA. The principle is straightforward: European data stays in Europe — under European jurisdiction, controlled by the organisation that owns it.
Marketing Goliath and the European Backup Alternative
European customers, despite having access to local technologies that represent genuine alternatives to US products, still rarely choose them. The primary reason is straightforward: marketing budget.
European vendors do not command the capital that US giants deploy. To put it in concrete terms: Veeam’s annual marketing spend exceeds Storware’s total recurring revenue. At a trade show, when a small European vendor’s booth sits beside a two-storey competitor pavilion with celebrity speakers, customers instinctively equate financial scale with technical superiority. That equation is frequently wrong.
The Psychology of the “Safe” Decision
Technology decision-makers have long operated under a version of the old IBM principle: nobody ever got fired for buying the market leader. A CIO choosing Veeam or Commvault is buying professional safety as much as software. If the system fails, there is cover. But that same CIO choosing a smaller European vendor faces a different risk calculus — any failure requires explaining why the globally dominant option was passed over.
US vendors also benefit from extensive partner networks with presence in every major market. When an international corporation needs a unified backup solution for offices in Paris, Warsaw, and Buenos Aires, it gravitates toward a vendor that can guarantee local support everywhere. European vendors — often with stronger architecture and greater flexibility — must compete not just on code quality, but against the logistical reach of globalisation.
The Gartner Magic Quadrant: Useful Guide or Compliance Shortcut?
The Gartner Magic Quadrant functions in enterprise IT as a near-oracle. For vendors, a Leaders designation is a ticket to multi-million-dollar contracts. But uncritical reliance on a ranking whose methodology and cultural DNA are deeply rooted in American corporate structures can be a trap for European buyers.
Gartner is not infallible. History offers cautionary examples of Magic Quadrant “stars” that faded faster than they generated returns. A position on the grid does not guarantee market longevity, architectural quality, or — critically — alignment with European compliance requirements.
Modern CIOs are changing the rules. Rather than relying exclusively on analysts, they are diversifying their intelligence sources. Platforms such as G2, TrustRadius, and LinkedIn provide unfiltered real-world user experience. Engineers increasingly run a Proof of Concept before any procurement conversation. This is a model where code quality wins, not marketing budget.
Think of Gartner as a Michelin guide. If you are a CIO without a strong internal technical team, the Quadrant is a useful starting point. But if your team can look under the hood and evaluate architecture independently — including how a vendor handles compliance with NIS2, DORA, and the CLOUD Act conflict — the Magic Quadrant becomes a reference point, not a mandate.
Key Takeaways
The choice between a US hyperscaler and a European provider has ceased to be a purely technical decision. It is a decision about operational sovereignty. Four things to carry forward:
- Jurisdiction matters more than location. Under the US CLOUD Act and FISA 702, data on a server in Warsaw belonging to a US provider is still subject to US law. Server geography is a latency decision, not a sovereignty decision.
- Regulatory compliance is now mandatory. NIS2 and DORA both require organisations to assess their providers’ exposure to non-EU government access demands. Not evaluating this is a documented compliance failure — not a theoretical risk.
- Scale is not the same as quality. Marketing budgets create a perception of security. Rigorous Proof of Concept testing is what reveals actual performance, architecture, and recovery capability under realistic conditions.
- Proximity equals speed. In a crisis, a transatlantic recovery bottleneck can push RTO toward the 24-day industry average. Local, policy-driven backup under your own jurisdiction is the shortest path to restored operations — and the strongest foundation for compliance with European law.
When you buy technology, do not buy peace of mind for the vendor — buy real control over your own data. In a digital world, the safest approach is to keep the keys to your own house in your own pocket.
Ready to take back control?
See how Storware protects your data — under European jurisdiction, on your terms.
Our team will walk you through a PoC tailored to your environment — whether you’re running VMware, Proxmox, OpenStack, Hyper-V, or a mix of all of them.
Frequently Asked Questions
What is the US CLOUD Act and does it affect European companies?
The CLOUD Act (Clarifying Lawful Overseas Use of Data Act, 2018) allows US law enforcement to compel US-based cloud providers — including Microsoft, Google, and Amazon — to hand over data stored anywhere in the world, regardless of physical server location. For European companies using these providers, this means data stored on a server in Frankfurt or Warsaw is still potentially accessible by US authorities. This directly conflicts with GDPR Article 48, which requires a formal international treaty before EU data can be transferred to non-EU authorities. The conflict is unresolved and creates legal risk for any European organisation relying on US-provider cloud storage for sensitive or regulated data.
How does NIS2 require companies to address CLOUD Act risk?
NIS2 (applicable since October 2024) requires essential and important entities to assess ICT supply chain security risks under Article 21, which explicitly includes evaluating whether cloud providers are exposed to non-EU government access demands. An organisation that has not conducted this assessment — and documented its findings — may already be non-compliant with NIS2, regardless of whether a CLOUD Act demand has ever actually occurred. Fines reach €10 million or 2% of global annual turnover for essential entities.
What does RTO mean and why does backup location affect it?
RTO — Recovery Time Objective — is the maximum acceptable time to restore systems and resume operations after an incident. Backup location directly affects RTO because data must physically travel from where it is stored to where it is needed. When backups are stored in local or European data centres, restoration happens at LAN or regional network speeds. When backups are stored in transatlantic cloud infrastructure, restoring large datasets (commonly tens of terabytes in enterprise environments) can take many hours to days — independently of any other complication. The 2025 industry average of 24 days of downtime after a ransomware attack reflects, in part, the operational bottleneck of remote recovery combined with infrastructure complexity.
Is a European backup solution really competitive with Veeam or Commvault?
Technically, yes — and in some dimensions it goes further. Storware Backup and Recovery provides agentless protection across VMware vSphere, Nutanix AHV, Proxmox, Microsoft Hyper-V, OpenShift Virtualization, XCP-ng, OpenStack, and other platforms under a single universal licence. For heterogeneous environments, this is a structural advantage that large US vendors — typically priced per platform or per workload — cannot match without significant cost multiplication. The gap between European and US backup vendors is primarily in marketing budget and partner network reach, not in architecture or capability.
What is DORA and which organisations does it apply to?
DORA — the Digital Operational Resilience Act (EU 2022/2554) — has been applicable across the EU since January 2025. It applies to all financial entities operating within the EU: banks, insurance companies, investment firms, payment institutions, and others. DORA requires these organisations to assess ICT provider concentration risk, evaluate confidentiality commitments of providers, and maintain documented exit strategies for critical ICT relationships. Cloud-hosted backup infrastructure falls squarely within scope. Financial entities that have not assessed their backup provider’s CLOUD Act exposure as a concentration risk are not fully DORA-compliant.
What is data sovereignty and is it different from data residency?
Data residency refers to the physical location of servers where data is stored. Data sovereignty is a broader concept — it refers to who has legal control over the data, and under which jurisdiction’s laws it falls. These are not the same thing. Data can be physically resident in a German data centre and still be subject to US jurisdiction if the provider is a US-incorporated company subject to the CLOUD Act. True data sovereignty requires that both the physical infrastructure and the legal jurisdiction of the provider are aligned with your compliance requirements. For European organisations under GDPR, NIS2, and DORA, this typically means choosing providers incorporated and operating exclusively under European law. The EDPB Guidelines 02/2024 on Article 48 provide the definitive regulatory interpretation of this distinction.
Sources & Further Reading
Research & Statistics
- Sophos (2025). State of Ransomware 2025. Based on 3,400 organisations across 17 countries.
- Sophos (2025). The State of Ransomware 2025 — Key Findings. Sophos Blog.
- IBM & Ponemon Institute (2024). Cost of a Data Breach Report 2024. Global average breach cost: $4.88M.
European Legislation (Official Texts)
- European Parliament & Council (2016). General Data Protection Regulation — Regulation (EU) 2016/679. EUR-Lex.
- GDPR-info.eu. Article 48 GDPR — Transfers or disclosures not authorised by Union law.
- European Data Protection Board (2024). Guidelines 02/2024 on Article 48 GDPR. December 2024.
- European Parliament & Council (2022). NIS2 Directive — Directive (EU) 2022/2555. EUR-Lex. Applicable from 18 October 2024.
- European Parliament & Council (2022). DORA — Regulation (EU) 2022/2554 on Digital Operational Resilience. EUR-Lex. Applicable from 17 January 2025.
- European Commission (2023). EU Data Act — Regulation (EU) 2023/2854. Applicable from 12 September 2025.
- EU Member States (2025). Declaration for European Digital Sovereignty. Berlin Summit, 18 November 2025.
Analysis & Background Reading
- Exoscale (2025). CLOUD Act vs. GDPR: The Conflict About Data Access Explained.
- Wire (2025). What the CLOUD Act Really Means for EU Data Sovereignty.
- Kiteworks (2026). Preventing US Government Access to European Data: CLOUD Act Guide.
