Agent-Based vs. Agentless Backup
Table of contents
- Agent-Based Backup: The Security Guard Inside the System
- Agentless Backup: Centralized, API-Driven Protection
- Agent-Based vs. Agentless Backup: Side-by-Side Comparison
- The Organizational Tension: Infrastructure vs. Development
- Hybrid Backup Strategy: The Enterprise Standard
- Compliance, Regulations, and the Modern Threat Landscape
- How Storware Bridges Both Worlds
- Choosing the Right Architecture: A Decision Framework
- Frequently Asked Questions
- Sources and References
The backup market has never been more competitive. Vendors promote agentless backup as the modern, lightweight approach, while others defend agent-based backup as the only way to guarantee deep application visibility and transactional consistency. But trends alone should never define your architecture. What should define it is your digital ecosystem, virtualization layer, regulatory landscape, and recovery objectives (RTO/RPO).
Consider a practical analogy. Imagine you need to secure a large retail store. You could install a centralized camera system monitoring every entrance and aisle — efficient coverage with minimal physical presence. Alternatively, you could station a professional guard walking between shelves, observing every detail — more precise, but more resource-intensive. In the world of enterprise data protection, that choice translates into a fundamental architectural question:
Is centralized, API-driven visibility enough, or do you need deep, system-level insight into every workload?
This article breaks down both approaches with the technical depth enterprise architects need, examines where each model excels and where it falls short, and explains why the answer for most organizations is a carefully designed hybrid.

Agent-Based Backup: The Security Guard Inside the System
Agent-based backup is a proven, battle-tested method. It involves installing dedicated software directly on each physical or virtual machine. This “digital insider” gains direct access to file systems, applications, databases, and OS-level processes — a level of visibility that no external system can fully replicate.
Agent-based solutions typically operate in two primary modes, each designed for a different recovery scenario.
File-Level Backup
File-level agents provide granular protection of specific files and folders. If a critical financial forecast disappears from a shared drive, a file-level agent can restore that single file within seconds — without touching anything else on the system. This approach is particularly effective for endpoint backup, file servers, user data protection, and environments with granular compliance requirements where you need to prove recovery capability at the individual document level.
Image-Level (Block-Level) Backup
When a major failure strikes, restoring individual files is not enough. Image-level backups can be performed either by in-guest agents or by hypervisor-level mechanisms depending on the platform. Instead of rebuilding the operating system, reinstalling applications, and reconstructing configurations manually, you restore the full image to new hardware or infrastructure. Downtime drops from days to minutes, which is critical for enterprises operating under strict SLAs.
Block-level agents carry significant technical responsibilities. They must track changed disk blocks between backup cycles (Changed Block Tracking), coordinate with OS services to ensure write-order consistency, handle open files and in-flight transactions, and maintain application awareness for databases like SQL Server or Oracle. File-level agents face their own challenges: managing locked files on production systems, maintaining data integrity during active workloads, and navigating complex filesystem hierarchies.
The Challenge: Operational Complexity at Scale
Agent-based backup provides unmatched depth of control — but becomes operationally complex as environments grow. In fast-moving infrastructure where DevOps teams provision dozens of VMs daily, manually installing and maintaining agents on every machine becomes a logistical bottleneck. The operational costs compound: deployment overhead across each new machine, continuous patching to maintain agent-OS compatibility, per-agent monitoring and troubleshooting, and CPU/RAM consumption inside every protected VM.
According to industry analysis, each agent also represents an additional attack surface (although centralized backup servers themselves must also be strongly secured as high-value targets). Poorly managed or outdated agents can introduce security vulnerabilities — unauthorized access points, potential data breaches, or pathways for malware propagation. In an era where the Veeam 2024 Ransomware Trends Report found that attackers target backup repositories in 96% of ransomware incidents, minimizing your security footprint matters more than ever.
Agentless Backup: Centralized, API-Driven Protection
When infrastructure scale outpaces what manual agent management can handle, agentless backup becomes the architecturally sound choice. Despite the name, it is not truly “agent-free.” Instead of deploying hundreds of individual agents, you operate a centralized backup engine that communicates directly with the hypervisor or platform layer through native APIs.
For VMware environments, this means integration with vSphere APIs for Data Protection (VADP). For KVM-based platforms like OpenStack, data transfer typically occurs via storage-layer snapshot mechanisms (such as Ceph RBD snapshots or Cinder volumes), sometimes coordinated through hypervisor integrations like libvirt. For container platforms like Kubernetes and Red Hat OpenShift, the engine works through the OpenShift API for Data Protection (OADP) operator and CSI snapshot capabilities.
Think of it as upgrading from individual security guards stationed in every room to a centralized control center with live feeds from every camera in the building. You gain complete visibility with a fraction of the operational overhead.
Why Agentless Scales
The architectural advantages of agentless backup compound as environments grow. New virtual machines and containers are discovered automatically — no manual agent installation required. All management flows through a single console, eliminating the per-VM maintenance burden. Backup processing tasks like hashing, compression, and deduplication are offloaded to proxy servers or the hypervisor layer, leaving zero resource footprint inside guest VMs. Deployment into dynamic, fast-scaling DevOps environments takes minutes rather than hours.
This makes agentless backup the natural fit for large virtual infrastructures, private and hybrid clouds, Kubernetes clusters, and any environment where machines are created and destroyed frequently.
Understanding the Trade-offs
Agentless backup does involve trade-offs that architects must account for. Snapshot-based backups can briefly stun highly loaded VMs during the snapshot creation phase, usually lasting milliseconds in modern hypervisors. By default, agentless backups produce crash-consistent snapshots; achieving application-level consistency requires additional mechanisms such as VMware Tools quiescing or QEMU Guest Agent integration for KVM environments. Granular database restore options may also be more limited without application-aware integration — a point that matters significantly for environments running critical SQL Server, Oracle, or SAP HANA workloads.
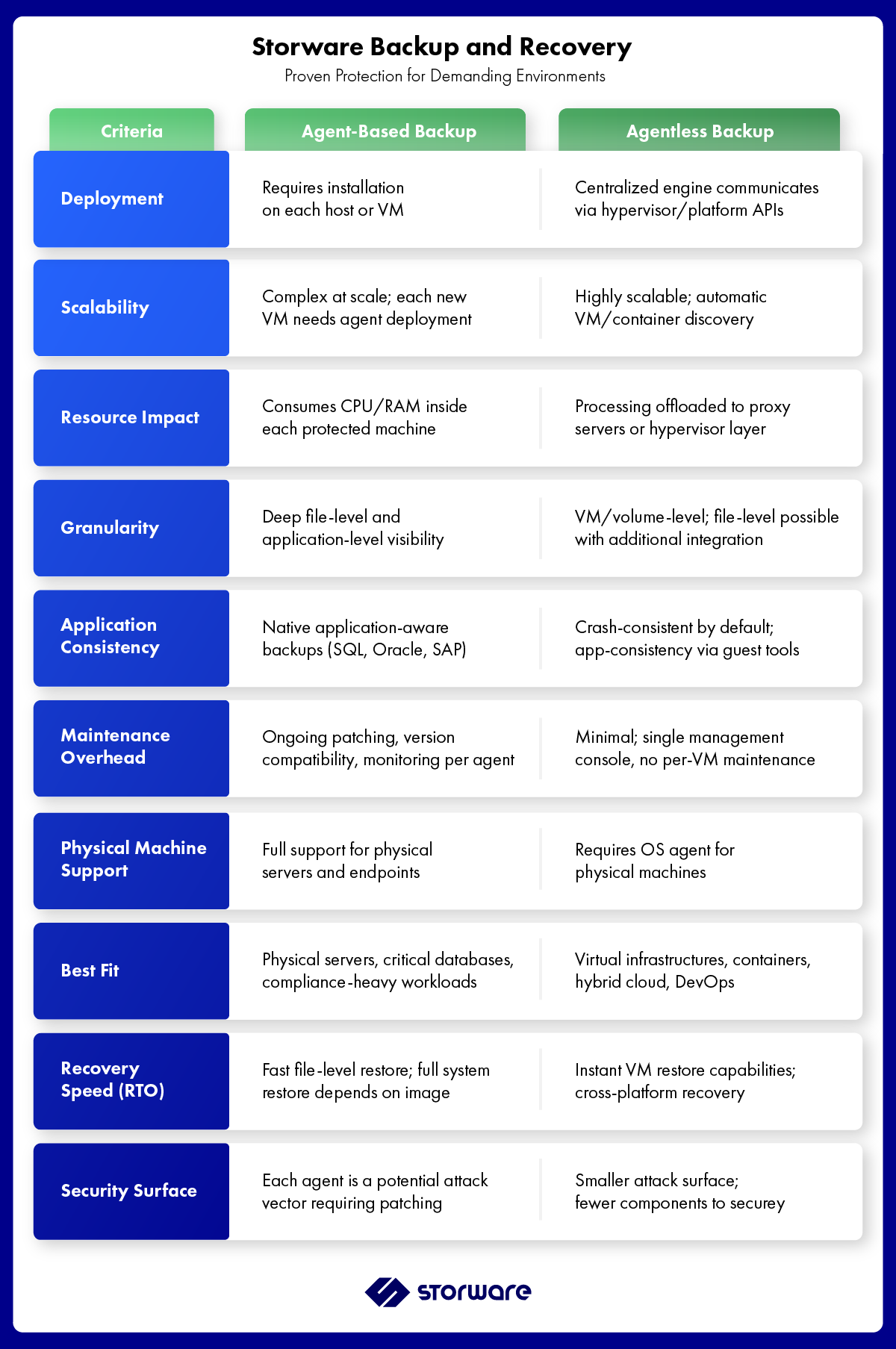
Agent-Based vs. Agentless Backup: Side-by-Side Comparison
The table below summarizes the key architectural differences to help you evaluate which approach — or which combination — fits your environment.
The Organizational Tension: Infrastructure vs. Development
The agent-based vs. agentless debate often mirrors an organizational tension that plays out in enterprise IT every day. Infrastructure administrators tend to favor agents because they deliver full control and full visibility — they can see exactly what the backup is doing inside every machine. Developers and DevOps engineers, on the other hand, resist agents because of performance overhead, deployment friction, and the operational drag of maintaining yet another piece of software on every workload.
Neither perspective is wrong. Backup architecture must be driven by infrastructure type, business criticality of each workload, compliance requirements, ransomware resilience strategy, and recovery time objectives — not by team preference alone.
And the ransomware dimension cannot be overlooked. Modern attacks increasingly target hypervisor layers and backup repositories directly. Sophos research found that in 94% of ransomware attacks, attackers specifically attempted to compromise backup repositories. The Veeam 2024 Ransomware Trends Report puts the figure even higher at 96%. A robust backup strategy today must therefore include immutable storage, air-gapping, and anomaly detection — regardless of whether the underlying architecture is agent-based, agentless, or hybrid.
Hybrid Backup Strategy: The Enterprise Standard
Modern IT environments are inherently heterogeneous. Most enterprises operate across on-premises infrastructure, multiple cloud providers, SaaS workloads, container platforms like Kubernetes and OpenShift, and physical endpoints. A one-size-fits-all backup approach simply does not work for this reality.
The Agentless-First, Agent-Where-Needed Model
The most effective enterprise backup model follows a clear principle: deploy agentless backup as the foundation and add agents only where deeper granularity or physical machine protection demands it. In practice, this means agentless backup handles the vast majority of virtual machines, containers, and cloud workloads — delivering configuration monitoring, compliance visibility, and scalable protection with minimal overhead. Agents are deployed selectively on systems that require it: SQL Server and Oracle database hosts where transaction log management and application-consistent quiescing are essential, high-value transactional systems with strict RPO requirements, physical servers and endpoints that fall outside the hypervisor layer, and workloads with specific compliance mandates requiring file-level audit trails.
This is not a compromise. It is an architectural optimization that matches the right tool to the right workload.
Agent-Assisted: Ephemeral Precision
A more advanced variant of the hybrid model uses temporary or ephemeral agents. These lightweight agents are deployed on demand to collect application metadata, manage transaction logs, or ensure snapshot consistency for a specific backup window — then remove themselves after execution. This preserves the simplicity and low overhead of agentless architecture while enabling application-aware precision exactly when it is needed.
Compliance, Regulations, and the Modern Threat Landscape
Regulatory frameworks have become a primary driver of backup architecture decisions. HIPAA in healthcare, PCI DSS in financial services, GDPR and NIS2 across the European Union — all demand detailed logging, auditability, and demonstrable recovery capabilities. These are not optional requirements, and backup solutions must be able to provide the evidence trails that auditors expect.
At the same time, the infrastructure landscape continues to evolve. Cloud-native workloads, Kubernetes clusters, microservices architectures, and Zero Trust security models all create new backup challenges. The global backup and recovery market continues to grow, driven by three converging forces: the ransomware epidemic (ransomware attacks increased 11% globally in 2024, reaching 5,414 documented incidents according to Veeam research), tightening regulatory pressure, and the ongoing digital transformation that makes data the core asset of every organization.
Organizations are no longer asking whether to implement enterprise backup. They are asking how to build a backup architecture that scales with infrastructure complexity while meeting compliance and recovery objectives.
How Storware Bridges Both Worlds
Storware Backup and Recovery was designed from the ground up around the principle that enterprise environments are heterogeneous — and backup architecture should reflect that reality. Rather than forcing organizations to choose between agentless simplicity or agent-based depth, Storware delivers both under a single universal license with a single management console.
Agentless: The Platform Core
Agentless backup forms the architectural foundation of Storware. The platform integrates natively with the widest portfolio of virtualization and container platforms available under one license, including VMware vSphere (via VADP), OpenStack with KVM (via Nova, Glance, and Cinder APIs with direct Ceph RBD integration), Red Hat OpenShift and Kubernetes (via OADP operator and helper pods for persistent volume backup), Nutanix AHV (with full support for Nutanix Files and Volume Groups), Proxmox VE, Microsoft Hyper-V, oVirt/RHV, Citrix Hypervisor, Oracle VM, and cloud platforms including AWS and Azure.
This breadth of platform support is not a feature list — it is a strategic differentiator. Organizations migrating from VMware following Broadcom’s acquisition and licensing changes can protect both their legacy VMware estate and their new target platform (OpenStack, Proxmox, Nutanix) from a single Storware deployment, eliminating the need for parallel backup solutions during transition.
Storware’s agentless engine supports both full and incremental backups, crash-consistent and application-consistent snapshots (via VMware Tools, QEMU Guest Agent, or pre/post snapshot command execution), automatic VM discovery and policy-based protection, and instant VM restore capabilities that mount backup data directly from the repository for near-zero RTO. Version 7.1 introduced cross-hypervisor restoration — enabling VM restores between different hypervisor types such as VMware vCenter/ESXi and OpenStack — a capability that directly supports migration and disaster recovery scenarios.
Agent-Based: Precision Where It Matters
Where agentless coverage needs to be complemented with deeper granularity, Storware provides targeted agent-based capabilities.
- Storware OS Agent is a lightweight agent for Windows, Linux, and macOS that enables file-level backup and granular recovery of specific folders and files. It supports full and incremental backups and is designed to coexist seamlessly with agentless VM protection — giving administrators the flexibility to protect individual file systems on machines that also benefit from VM-level agentless backup.
- Hyper-V Agent is installed directly on Hyper-V hosts, enabling secure communication between the Storware server and the Hyper-V virtualization infrastructure for host-level backup operations.
Ransomware Resilience Built In
Storware’s architecture includes immutable backup storage support across multiple destinations, ensuring that backup data cannot be modified or deleted by ransomware — even if attackers gain administrative access to production systems. Combined with policy-based automation for scheduling and retention, synthetic full backup generation, and support for air-gapped and tiered storage destinations (local filesystem, object storage, tape libraries, and enterprise backup providers like Dell Data Domain via DD Boost), Storware delivers the layered defense that modern ransomware resilience demands.
The result is a platform where organizations can choose agentless backup for virtual infrastructure efficiency, agent-based backup for precision and application-level protection, or a hybrid architecture aligned with enterprise risk management — all managed from one console, under one license.
Choosing the Right Architecture: A Decision Framework
Agent-based vs. agentless backup is not a battle of old versus new. It is a question of scale, performance, compliance, business continuity objectives, and risk tolerance. The right answer depends on your specific environment.
Choose agentless as your foundation when you operate primarily virtualized or containerized workloads, need to scale backup coverage dynamically as infrastructure grows, want to minimize operational overhead and security surface area, and require a single management plane across multiple platforms.
Add agent-based backup selectively for physical servers and endpoints outside the hypervisor layer, critical databases requiring transaction-level consistency, workloads with specific regulatory requirements for file-level audit trails, and any system where deep OS-level visibility is a compliance necessity.
In today’s complex IT environments, the real competitive advantage lies not in choosing one side of this architectural debate, but in designing a backup strategy that precisely matches each workload’s protection requirements while remaining operationally manageable and resilient against modern threats.
At Storware, we empower businesses with a proven, expert-driven platform designed to deliver simplified, scalable backup across the most demanding environments. Enterprise-ready backup. Simplified. Scalable. Proven.
Ready to see how Storware handles hybrid backup across your entire infrastructure?
Start with a free Community Edition or request a 60-day full-feature trial with complete installation and configuration support. Visit storware.eu/licenses to get started, or explore the full platform architecture at storware.eu/blog/storware-backup-and-recovery-architecture/.
Frequently Asked Questions
- Is agentless backup more secure than agent-based backup?
Agentless backup generally presents a smaller attack surface because there are fewer software components installed across your infrastructure. Each agent on a VM is a potential entry point that requires patching and monitoring. However, security ultimately depends on implementation: immutable storage, access controls, and encryption matter more than the agent model itself. The strongest security posture combines agentless architecture with immutable backup destinations and air-gapped storage tiers.
- Can you combine agent-based and agentless backup in one environment?
Yes, and most enterprise environments should. A hybrid approach uses agentless backup as the foundation for virtual machines and containers, then adds agents selectively for physical machines, critical databases, or workloads requiring file-level granularity. Platforms like Storware support both approaches under a single license and management console, so there is no additional complexity or cost in running a hybrid architecture.
- What is the performance impact of backup agents on production VMs?
Backup agents consume CPU and RAM inside each protected VM. The impact varies depending on the agent’s efficiency, backup schedule, and the VM’s available resources. In resource-constrained or high-load environments, agent overhead can be noticeable during backup windows. Agentless backup eliminates this entirely by offloading all processing to external proxy servers or the hypervisor layer.
- Does agentless backup work for physical servers?
No. Agentless backup requires a hypervisor or platform API to access data. Physical servers, endpoints, and bare-metal machines need an OS-level agent for backup. Solutions like Storware address this by offering a lightweight OS Agent for Windows, Linux, and macOS alongside their agentless VM protection.
- How does agentless backup handle application consistency for databases?
Agentless backup produces crash-consistent snapshots by default. For application consistency, the backup engine triggers quiescing mechanisms within the hypervisor layer — such as VMware Tools for vSphere or QEMU Guest Agent for KVM/OpenStack. These mechanisms coordinate with the guest OS to flush application buffers and ensure a consistent state before the snapshot is taken. For workloads requiring full transaction-log-level consistency (such as Oracle or SQL Server), an agent or agent-assisted approach is typically recommended.
- What should I look for in a backup solution for multi-hypervisor environments?
The critical factor is unified management under a single license. Many backup vendors charge per platform or per VM, and managing separate tools for VMware, OpenStack, Kubernetes, and physical machines creates operational complexity. Look for a solution that supports your current platforms and your target platforms (especially important during hypervisor migrations), offers both agentless and agent-based options, includes immutable storage support, and provides instant restore and cross-hypervisor recovery capabilities.
Sources and References
- Veeam 2024 Ransomware Trends Report — 96% of ransomware attacks target backup repositories.
- Sophos State of Ransomware 2025 — 94% of attacks attempted to compromise backup infrastructure.
- Veeam 2024 Data Protection Trends Report — 75% of organizations experienced ransomware in the past year.
- Storware Backup and Recovery Documentation — docs.storware.eu
- Storware Backup and Recovery Architecture Overview — storware.eu/blog/storware-backup-and-recovery-architecture/
